Top SBC Vendors in 2026: The Ultimate Comparison Guide
- July 12, 2025
- 11 Mins Read
- Listen

Service providers running a VoIP business are often on the lookout for the best unified communication tools. That’s why here in this post, we are discussing Session Border Controllers, which are critical in protecting, managing, and optimizing VoIP traffic. We will understand the basics of SBCs and explore the top 10 SBC vendors in 2026, along with what features to look for to help you decide.
What is a Session Border Controller?
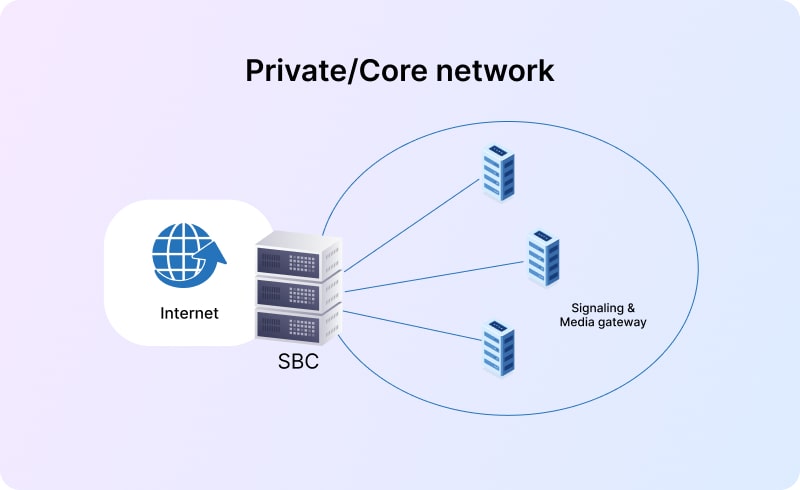
A session border controller is a specialized device, either hardware or software, that sits at the border or edge of a VoIP network and governs all voice sessions to protect them from threats and attacks. Let’s consider a real-world scenario of a call center that connects hundreds to thousands of calls per day. To make sure those calls do not face drops or other quality issues and are not attacked by malicious actors, the call center implements an SBC. The SBC encrypts those calls, ensures that only legitimate traffic gets through, and ensures interoperability between systems from different vendors.
In simple words, we can say that an SBC, in this case, acts as a first line of defense and an effective tool for smooth interconnection.
Key Features to Look for in an SBC Vendor
Different SBC vendors offer session border controllers with a varying set of features; however, some key features are important to have.
Check Security Capabilities
The primary role of deploying session border controllers within VoIP networks is to ensure security. This is the reason why you need to ensure the following points:
- Does the SBC protect against SIP-based threats? It should be able to block spoofed calls, malformed SIP packets, and suspicious traffic before it causes harm.
- Does the SBC support TLS, SRTP, and DoS/DDoS protection, along with fraud detection? While the TLS hides the call setup info from hackers, SRTP prevents the decoding of the data stream even if someone intercepts it. Additionally, DoS and DDoS protection are required to prevent flooding attacks that can overwhelm the VoIP service. Last but not least, the SBC should be able to detect abnormal call patterns using behavioral algorithms.
Ensure Interoperability
The interoperability feature of SBCs ensures that different VoIP systems talk to each other seamlessly. For example, suppose a business is using a SIP trunk from carrier A, a hosted PBX from vendor B, and a softswitch from vendor C. In that case, these systems might face SIP header mismatches, codec negotiation issues, and NAT traversal problems. Here, an SBC works like a translator and resolves all these issues.
Build for Future Expansion
A good SBC vendor should offer you the flexibility to pay for the capacity you need right now and upgrade when required. In other words, the SBC should scale with your business without requiring much effort from your side. Virtual SBCs like REVE allow you to scale up your capacity as much as needed with additional servers.
Top SBC Vendors in 2026: Best Session Border Controllers
Now let’s learn about some leading SBC vendors, their strengths, and who they’re ideal for.
REVE Session Border Controller (REVE SBC)

REVE Session Border Controller is a trusted choice for modern IP businesses looking to secure communications, optimize operations, and deliver high-quality voice traffic. The solution highlights a distributed architecture ensuring network resilience and supports real-time billing with intelligent routing.
Key Highlights
- Massive scalability with the capacity to handle up to 70,000 concurrent calls from a single server
- Offers both Access SBC (A-SBC) and Interconnect SBC (I-SBC) to meet your specific business needs.
- Integrated real-time billing with a mobile-responsive interface.
- Effectively handles heavy loads and defends against DoS attacks.
Ideal for
It is an ideal choice for VoIP service providers, telecom carriers & operators, hosted UC & cloud PBX providers, large enterprises, and wholesale voice businesses.
Ribbon SBC

This one is also a carrier-grade SBC with high reliability and scalable deployment options. Ribbon offers a wide range of SBC models, out of which SBC SWe (software) and SBC 5400 (hardware) are quite popular.
Key Highlights
- Strongly embraced virtualization and cloud deployments with its SBC Software Edition (SBC SWe) and SBC Cloud Native Edition (SBC CNe)
- Built for high availability and robust performance, even under heavy loads or attacks
- Ribbon’s Application Management Platform (RAMP) provides a centralized solution for managing multiple Ribbon SBCs
Ideal For
Large ISPs or enterprises seeking robust security, rich SIP interoperability, and proven performance can opt for this one.
Audio Codes

AudioCodes is particularly well-regarded for its Session Border Controllers (SBCs), offering both virtualized (SBC SWe) and cloud-native (SBC CNe) versions. Their popular SBC models include Mediant 800, Mediant VE, and Cloud Edition.
Key Highlights
AudioCodes has a long-standing and deep partnership with Microsoft, providing certified solutions for Microsoft Teams Direct Routing and Operator Connect.
Ideal For
They offer tailored solutions ranging from small office deployments to large-scale carrier networks.
Oracle

Oracle is another major player in the telecom software and hardware space. Their Session Border Controllers are a core part of their product portfolio, and their popular products include Oracle SBC and Enterprise Communications Broker.
Key Highlights
- Oracle offers both purpose-built hardware appliances and virtualized/cloud-native software editions (VNF – Virtual Network Function).
- Like Ribbon and AudioCodes, Oracle SBCs are certified for Microsoft Teams Direct Routing and other leading UCaaS and CCaaS platforms
Ideal For
If you are a service provider looking to manage complex SIP routing and billing policies, then Oracle could be an option you can explore.
Cisco

A giant in the networking and telecom space, Cisco offers an SBC solution with the name CUBE, i.e., Cisco Unified Border Element. It’s software that runs on Cisco’s widely deployed Integrated Services Routers (ISRs) and Aggregation Services Routers (ASRs), as well as virtual platforms. CUBE is a very popular choice for enterprises implementing Microsoft Teams Direct Routing.
Key Highlights
- Can be deployed on Cisco ISR/ASR routers (hardware-based) or as a virtual CUBE in cloud/data center environments.
Seamless integration with Cisco Unified Communications Manager (CUCM), Microsoft Teams, Zoom, and third-party platforms.
Ideal For
It is perfect for enterprises using Cisco UC (CUCM), organizations migrating from PSTN to SIP, Multinational corporations, and various Cisco-centric environments.
TelcoBridges

TelcoBridges heavily emphasizes software-only SBCs. This means their solutions can run on standard servers, in virtualized environments, or on public clouds, offering great flexibility.
Key Highlights
- Their ProSBC is designed for carrier-grade performance, handling a high volume of concurrent calls (up to 60,000 sessions on a single server, with more via scaling.
- TelcoBridges offers “FreeSBC,” which is essentially a free version of their ProSBC software, typically for smaller deployments.
Ideal For
This can be a good choice for smaller to mid-sized service providers, wholesale carriers, and enterprises.
InGate Systems

With a strong focus on enabling secure and reliable SIP (Session Initiation Protocol) communications for businesses, Ingate Systems has a long history in the IP communications and security space.
Key Highlights
- Their Enterprise Session Border Controllers (E-SBCs) are branded as SIParator®. They offer their SIParator products as both hardware appliances and software versions that can be deployed on customers’ own hardware or virtual machines.
- A key aspect of Ingate’s approach is the tight integration of SBC functionality with traditional firewall/router capabilities. Their SIParator devices often act as both a firewall and an SBC.
Ideal For
It’s a useful option for enterprises with Firewalls/NAT devices, small to mid-sized businesses, hosted PBX & UCaaS providers, ITSPs, and SIP trunking providers.
Sansay

Sansay specializes in providing high-performance, software-based Session Border Controllers (SBCs) serving a global base of hundreds of service providers, including wholesale, prepaid, hosted business, residential, and wireless operators.
Key Highlights
- Sansay’s flagship product, the VSXi Session Controller, is built from the ground up as a software-only solution designed to run on commercial off-the-shelf (COTS) Intel-based servers and Linux operating systems.
- They also have offerings like the WebSBC™ that specifically address the challenges of connecting WebRTC applications to traditional SIP networks.
Ideal For
If you’re offering hosted VoIP or SIP trunking and want rich APIs and real-time CDR access, then Sansay is a great choice.
Metaswitch

Another significant player, particularly known for its cloud-native communications software solutions for service providers. In July 2020, Microsoft acquired Metaswitch to bolster its Azure for Operators strategy. As of March 4, 2026, Alianza, a leading cloud communications platform for service providers, completed its acquisition of Metaswitch from Microsoft.
Key Highlights
- Designed from the ground up for NFV and cloud environments – ideal for deployment on private, public, or hybrid clouds.
- Supports deployment on VMs, containers (e.g., Kubernetes), and bare metal, making it future-proof and DevOps-friendly.
Ideal For
Tier-1 and Tier-2 Telecom Operators, VoIP & Mobile Network Operators, Carriers Transitioning to 5G/IMS
Conclusion
There are so many options available in the market, and some of the popular ones are listed above in this post. While every vendor comes with its own technical specifications and claims to be the best, choosing the right one can be overwhelming. But here’s the catch: just understand your own requirements first, then the process of choosing the right SBC vendor will become a lot simpler.
Whether you’re a global telecom operator needing bulletproof scalability or a growing ITSP looking for cost-effective control, there’s a vendor built precisely for that. The smartest approach is not to chase the ongoing trends or go with the popular names. Match the capabilities of the SBC to your specific goals, your technical requirements, and your customer expectations.
It is always a good idea to assess real-world use cases, ask for free demos or trials for a certain period, and engage with their support teams to resolve all the queries you have. Remember, voice communication is evolving at a skyrocketing speed. You need to choose a partner and not just a product to achieve success in today’s increasingly digital voice economy.
Secure Your VoIP Network with REVE SBC : Try It Today!
Whether you’re managing inter-carrier traffic, deploying hosted PBX services, or operating a global voice platform, REVE SBC provides the flexibility and reliability you need. It combines carrier-grade features with user-friendly management and affordable licensing. Here are some key highlights again:
- Built to manage high call volumes
- Ensures complete control over SIP traffic
- Offers real-time call monitoring
- Supports SIP normalization and NAT traversal
- Performs media handling and intelligent call routing
- Advanced security against fraud and DDoS attacks
- Seamless interconnection with diverse VoIP systems
- Ready to grow without compromising quality or security
REVE SBC stands out as an affordable SBC for telecom and also a reliable and feature-rich choice for VoIP service providers, carriers, and enterprises.
Book a free demo or request a trial today to see how REVE SBC can safeguard your network and boost voice performance.
Frequently Asked Questions
How are hardware and virtual SBCs different?
As the term suggests, hardware SBCs are physical appliances that are installed within the premises of a business. Typically, large enterprises or telecom carriers prefer hardware SBCs so that they get full control over their infrastructure.
Virtual SBCs, on the other hand, run on virtual machines or in cloud environments. These are also called cloud SBCs or software-based SBCs. When compared with hardware SBCs, virtual SBCs offer more flexibility, scalability, and cost-effectiveness, which is suitable for service providers and modern VoIP setups.
Do SBCs work towards improving call quality?
While the primary role of SBCs is to provide security and interoperability, they also work towards improving call quality in various significant ways. This includes prioritization of voice traffic, bandwidth management, CAC i.e. Call Admission Control, jitter buffer management, codec transcoding, and call rerouting.
Are cloud SBCs secure?
Yes, reliable cloud SBC vendors implement robust security features like behavior-based alerts, IP whitelist/blacklist, 2FA, and hang-call detection to minimize risks and prevent unnecessary billing.
Which SBC comes with an integrated billing system?
REVE SBC is one of the few that comes with an integrated VoIP billing system. It allows service providers to manage billing, call routing, and session control- all from a single platform.
Are SBCs effective in preventing telecom fraud?
Absolutely, SBCs are a frontline defense against telecom fraud. With features like IP whitelisting, rate limiting, and real-time call monitoring, SBCs efficiently detect and block abnormal call patterns, unauthorized access, and toll fraud attempts. This helps prevent revenue loss and protects both carriers and end-users.

























